
[ad_1]
The time period “cloud computing” will get thrown round rather a lot today. However what does it actually imply? Behind the buzzword lies actual applied sciences, like infrastructure-as-a-service (IaaS), that present scalable on-demand computing, storage, and networking.
Nevertheless, migrating to the cloud is like shifting your group into an infinitely scalable but invisible workplace tower. 75% of the companies state that over 40% of their information saved within the cloud is delicate. Neglecting safety right here leaves a variety of firm data susceptible to threats, like unauthorized entry, exploits, and non-compliance.
The excellent news is that whereas “the cloud” appears ephemeral, with the precise foundations and finest practices, you’ll be able to successfully safe IaaS environments.
On this information, we’ll share 12 important tricks to lock down safety in your unmanaged cloud servers, VMs, containers, storage, and companies, benefiting from the quick progress that cloud environments provide. Let’s get began.
1. Disallow Root Password Logins
Probably the most frequent strategies that attackers use to achieve unauthorized entry to servers is by brute forcing weak passwords for extremely privileged accounts like root or administrator.
To know why, think about your self as a malicious hacker. In case your objective is to get right into a system and achieve entry to delicate information, you’ll seemingly begin by trying to brute-force the foundation password (repeatedly making an attempt completely different passwords till the right one is discovered). If the try is profitable, you achieve entry to the foundation account, which has the very best stage of system permissions out there, permitting full management over the server.
The factor with brute pressure assaults is that this: weak passwords may be cracked simply with the precise instruments— and even sturdy passwords may be cracked by a affected person, decided hacker.
What should you fully disable password-based root login and as an alternative depend on SSH key-based authentication instead?
SSH
Safe Shell Protocol (SSH) is a cryptographic community protocol for operating companies securely via an unsecured community. It’s principally used for command-line executions and distant logins.
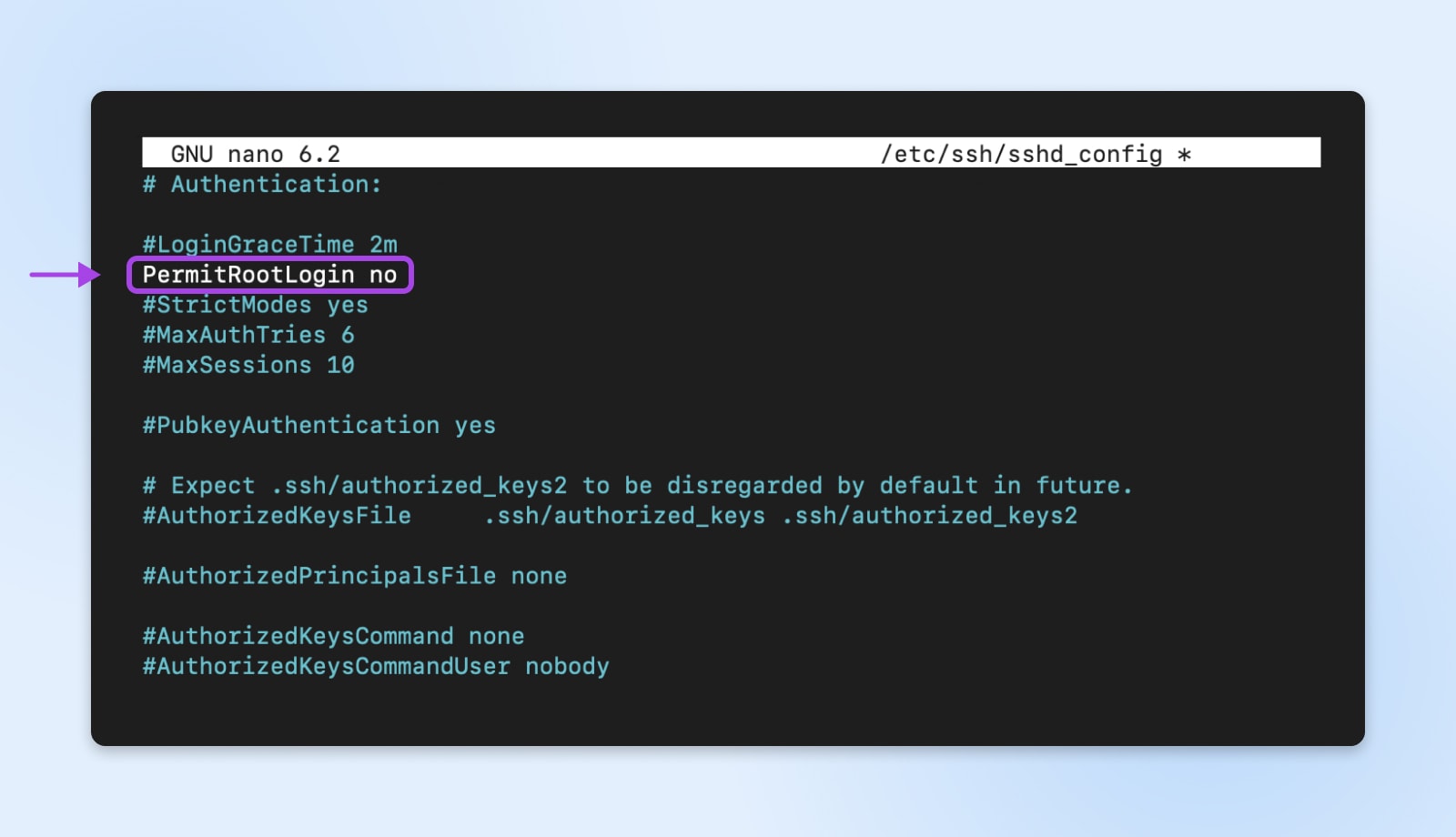
This configuration may be discovered within the /and many others/ssh/sshd_config file in your Linux server.
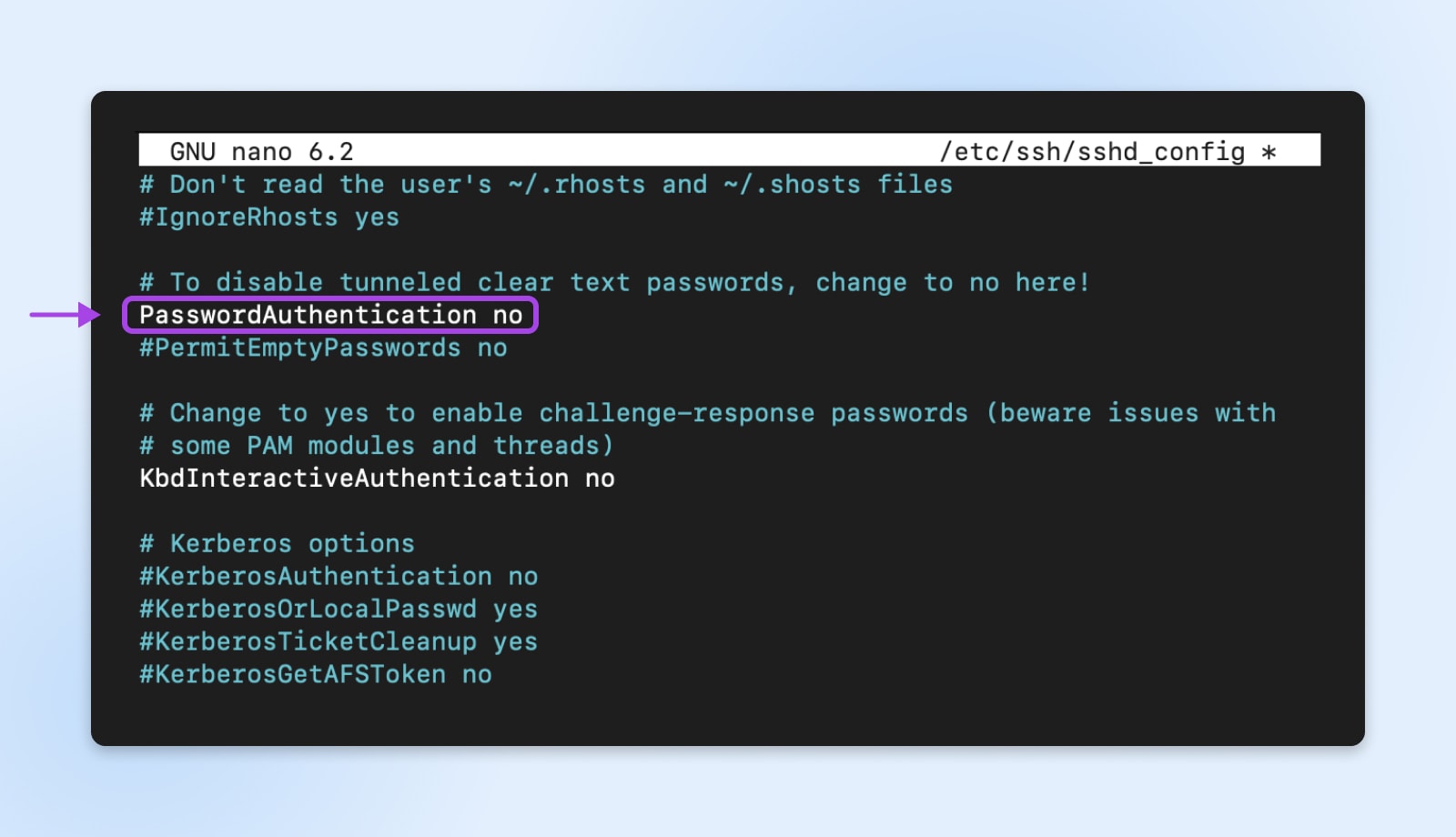
This is a superb step in the precise path. SSH keys use uneven encryption, which means a personal and public key pair – moderately than a password – is used to authenticate login makes an attempt.
You possibly can go a step additional and disable root login over SSH to stop individuals from trying brute-force on root. This may be executed by altering the PermitRootLogin to no in the identical file.
The personal key, because the identify implies, is saved privately by the approved person and saved on their laptop. The corresponding public secret’s then saved on the server related to that person’s account.
In the course of the login course of, the keys use cryptographic strategies to validate the approved connection with out revealing the precise personal key. This methodology successfully protects in opposition to brute pressure assaults for the reason that login can’t be compromised via mere password guessing.
Get Content material Delivered Straight to Your Inbox
Subscribe to our weblog and obtain nice content material identical to this delivered straight to your inbox.
2. Allow Automated Safety Upgrades
All software program comprises vulnerabilities: some recognized and a few but undiscovered.
Attackers are continually probing packages for brand spanking new bugs that permit them to achieve entry and management. When vulnerabilities are discovered and glued by the software program distributors, they publish safety updates.
For those who’re manually upgrading methods, hackers might use the chance the place your methods are nonetheless susceptible and achieve entry. However with auto upgrades, you’ll be able to depart that stress behind.
For instance, if a vulnerability is found in a programming library utilized by your cloud database software program (e.g., SQLite), hackers may quickly be taught of it and launch assaults. But when your database servers are set as much as routinely set up safety updates as they’re revealed, it should obtain and apply the patch to repair the problem earlier than any compromise happens.
Additionally, the method of auto-upgrades may be custom-made to use safety patches on a set schedule solely after they’ve been adequately examined. For mission-critical methods, you could select to stage and check updates earlier than broad deployment. Automation removes the burden of handbook intervention whereas nonetheless protecting your cloud entry safe.
3. Set up And Configure Fail2ban
Brute pressure assaults are available many kinds, focusing on varied community companies. Past abusing logins like SSH, we additionally want to think about net functions, e mail servers, databases, and extra, which can be susceptible to password-guessing makes an attempt.
That is the place intrusion safety instruments like Fail2ban are available very helpful.
Fail2ban works by repeatedly monitoring log recordsdata generated by community companies and parsing them for indicators of repeat failed entry makes an attempt which are indicative of automated brute forcing. When failed makes an attempt exceed a configurable threshold, Fail2ban will routinely replace system firewall guidelines to dam the supply IP deal with accountable, stopping additional abuse of that service.
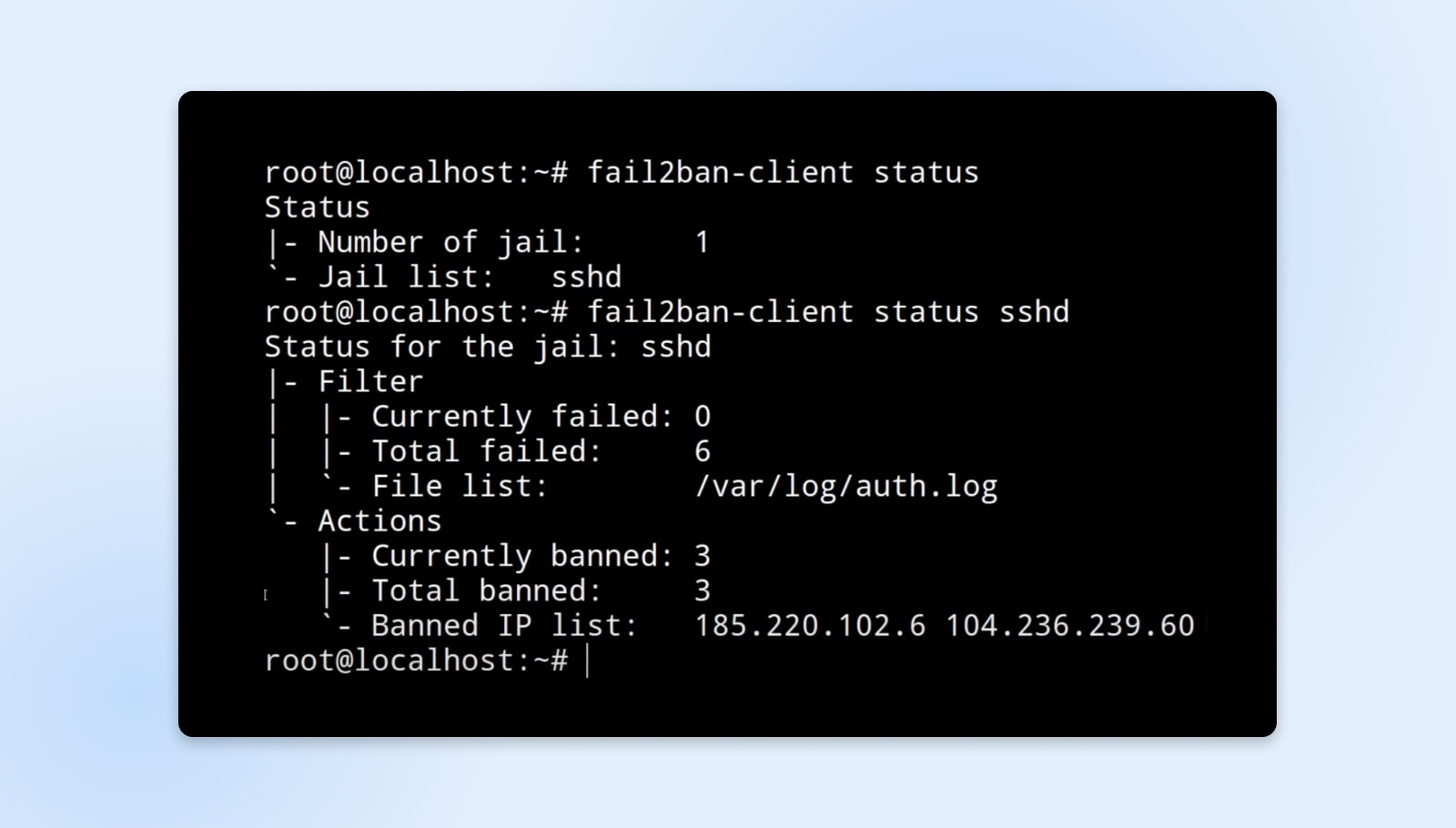
To place this in perspective think about this:
Alice configures Fail2ban on her net server to observe authentication failure logs. If an IP makes 5 failed login makes an attempt to the admin console in underneath two minutes, indicating a possible assault, Fail2ban will routinely block that IP from accessing the online software for 10 minutes. This protects the supply of the app for reputable customers whereas deterring malicious actors.
The non permanent IP bans will help decelerate attackers actively making an attempt to guess credentials or discover exploits. Fail2ban is extremely customizable as nicely — you’ll be able to fine-tune the companies monitored, thresholds earlier than banning, length of bans, logging parameters, and extra. This flexibility permits it to be extensively leveraged to guard in opposition to brute-force dangers throughout most cloud workloads.
4. Configure Cloud Safety Teams As Firewalls
Whereas instruments like Fail2ban function on the particular person server stage to guard in opposition to assaults, we should additionally think about safeguarding cloud sources on the community layer. Cloud platforms at DreamHost are pre-configured to be safe.
Together with this, DreamHost supplies you with a configurable digital firewall so you’ll be able to resolve what visitors is accepted or rejected other than the default settings.
For instance, net servers usually solely want to simply accept inbound HTTP and HTTPS connections over ports 80 and 443. So, the safety group assigned to those hosts could be configured to dam all different protocols and port mixtures by way of deny-by-default guidelines. Equally, outbound visitors could be narrowed right down to solely what is totally important for that operate.
Cautious configuration of safety teams acts as the primary line of protection, permitting solely approved ingress and egress visitors to achieve your cloud servers and companies based on finest practices of least privilege entry.
5. Contemplate Implementing An Intrusion Detection System

Whereas we’ve mentioned measures to proactively block unauthorized entry makes an attempt and forestall exploitation of recognized vulnerabilities, expert attackers should discover methods to penetrate defenses via as-yet-unknown flaws.
In these circumstances, detection as early as attainable turns into vital.
That is the place an Intrusion Detection System (IDS) can present immense worth — repeatedly monitoring methods for suspicious actions indicative of a breach. IDS options are available two fundamental kinds:
- Community IDS (NIDS): Analyzes community packets inspecting for malicious payloads like viruses or recognized assault patterns. Usually used to detect malware propagation and network-focused hacking makes an attempt.
- Host IDS (HIDS): Displays actions, configurations, and logs on a person server. Checks for indicators of tampering, unauthorized modifications, or integrity violations.
“To forestall brute-force assaults, multi-factor authentication, safe session insurance policies, fee limiting, computerized timeouts and a well-rounded intrusion detection system (IDS) ought to be applied. Additionally embrace using safe and random session identifiers, storing session information in safe areas like HttpOnly and Safe cookies, and implementing mechanisms to detect and forestall unauthorized session entry.”
— Jesse Befus, Managing Director, Enterprise Identification & Entry Administration at ATB Monetary
A well-liked instance used for Linux environments is Tripwire. It maintains an in depth baseline database of file attributes like permissions, hashes, metadata, registry entries, and extra for the host. At periodic intervals, it compares the present state in opposition to this baseline to examine for any unauthorized modifications that might point out foul play.
For instance, an attacker exploits a vulnerability to get shell entry on one of many net servers. He makes an attempt to interchange web site recordsdata with a malicious model that steals buyer fee information. As quickly as this alteration is made, Tripwire detects the change throughout its subsequent scheduled integrity examine. It alerts the administrator concerning the surprising webroot modification, permitting them to analyze the breach earlier than main harm happens.
With out Tripwire, such an assault might have gone unnoticed permitting the attacker to stealthily gather buyer data over an prolonged interval. Intrusion quickly detected is intrusion quickly contained!
As they are saying, “prevention is good however detection is a should,” and that’s the place cloud IDS choices ship immense worth to maintain your information safe.
6. Leverage Knowledge Encryption Extensively
To this point we’ve mentioned a number of layers of safety controls with the objective of stopping unauthorized entry to your cloud servers. Nevertheless, a basic information safety tenet is that prevention might fail, however encryption serves as a final line of protection.
Even when all different safeguards are bypassed and cloud servers get efficiently breached, encryption ensures saved information like SQLite databases, archives, and file shares stay protected and unusable to attackers. This is applicable to data-in-transit as nicely which ought to be encrypted throughout flows throughout networks.
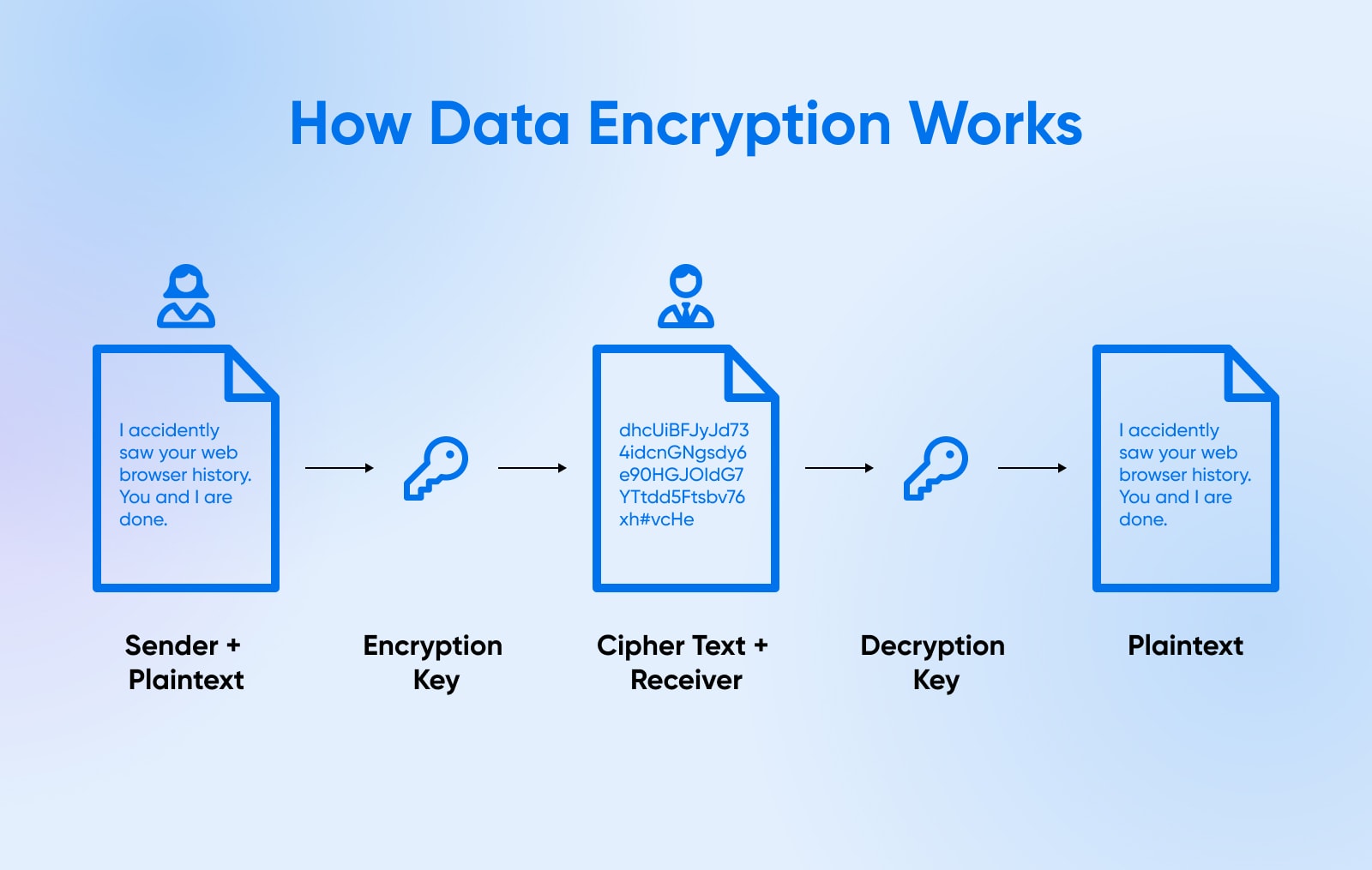
Encryption broadly falls into two classes:
- Uneven: Makes use of a public/personal key pair the place something encrypted with the general public key can solely be accessed by way of the matched personal key and vice versa. Typically used for safe connections.
- Symmetric: A shared secret secret’s used to encrypt and decrypt information. Used for environment friendly bulk encryption of information at relaxation as the identical key encrypts/decrypts.
If all different defenses fail, encrypted information foils the attacker’s objectives. What good is breaching a cloud database server if all data are gibberish with out the decryption key?
7. Schedule Common Safety Audits
We have now now coated varied preventative and detective controls to safe cloud infrastructure and information at relaxation. Nevertheless, an overlaying apply that connects the dots throughout all of them is routine safety audits.
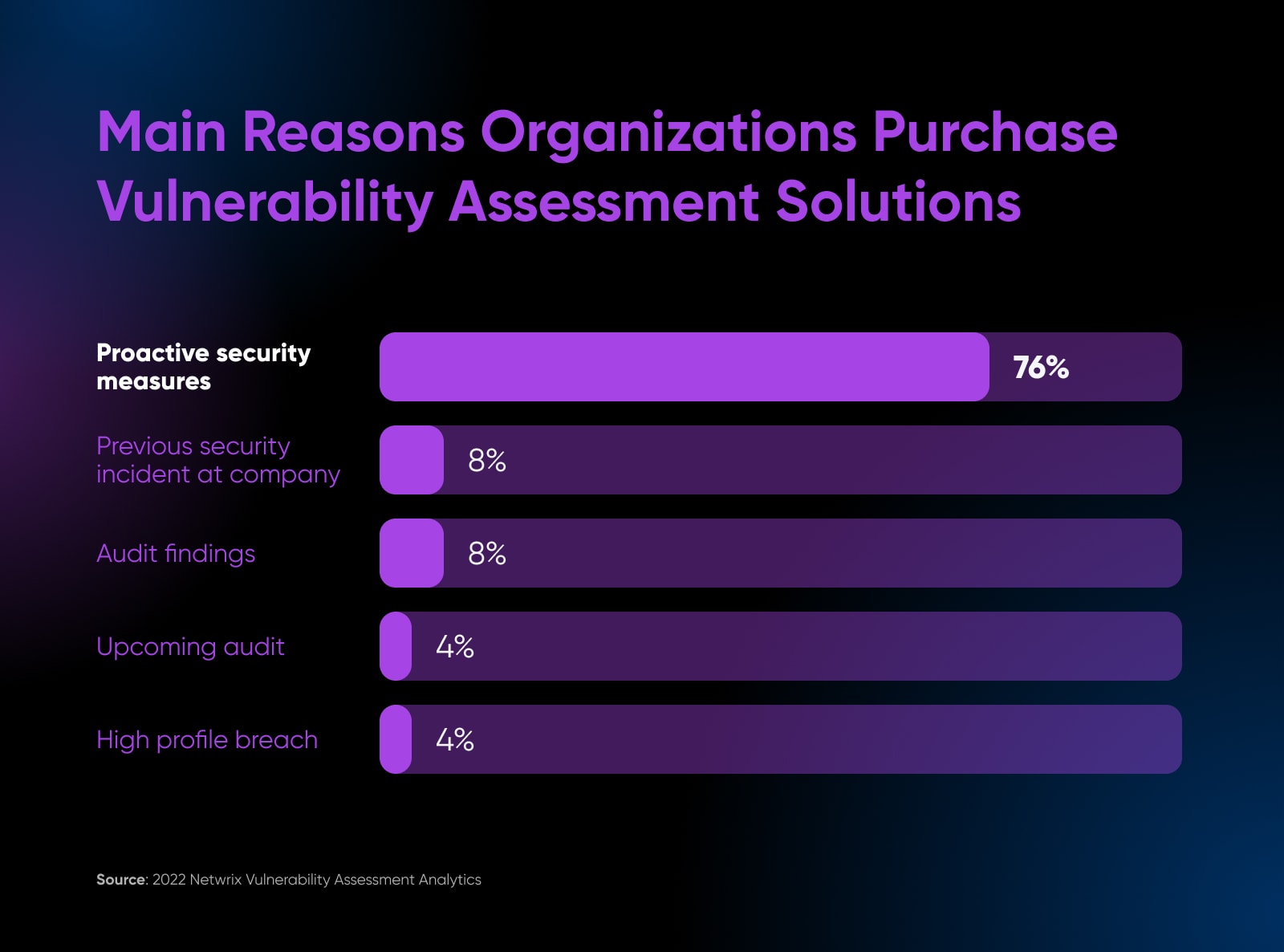
76% of the surveyed firms observe an everyday safety audit protocol to be proactive about safety points.
Audits serve a number of invaluable functions:
- Validate that controls are correctly applied as meant.
- Determine if any deficiencies or gaps want enchancment.
- Quantify and prioritize residual danger exposures.
- Uncover unknown vulnerabilities not seen in any other case.
- Present an up to date snapshot of present safety posture.
Principally, audits inform in case your documented cloud practices precisely mirror actuality.
You possibly can implement casual self-serve audits as a part of every day administration or schedule exhaustive formal assessments yearly relying on program maturity.
Consider these routine cloud safety audits as obligatory “well being exams” that discover danger areas and validate profitable practices so corrective actions may be taken earlier than one thing goes improper.
8. Implement Identification And Entry Administration
Now that we’ve mentioned safeguards deployed instantly inside the cloud infrastructure itself, the subsequent logical layer we progress to is managing administrative entry.
With out identification and entry administration (IAM) performing as cloud gatekeepers, attackers would merely goal person credentials subsequent to bypass infrastructure defenses via reputable entry channels.

That’s why a strong IAM program turns into the muse for who can entry cloud environments and information inside prescribed permissions — granting solely important privileges.
Among the most necessary parts of an IAM embrace:
- Central listing companies: Keep person accounts and roles in a central listing like Lively Listing with single-sign vs. regionally on particular person servers. Enforces entry revocation, password insurance policies, and consolidation.
- Precept of least privilege: Customers are matched to roles and teams that map to the smallest subset of methods and permissions wanted for operate vs. blanket entry. Minimizes publicity blast radius if accounts are compromised.
- Sturdy authentication: Passwords augmented with multi-factor authentication to entry cloud admin consoles and infrastructure. Reduces brute pressure susceptibility by necessitating extra components like tokens or biometrics when authenticating classes.
- Entitlement administration: Entry assignments and elevations tracked, offering visibility into permissions. Automated entry opinions mixed with routine entitlement reporting to prune pointless assignments over time.
- Audit logs: Exercise logging with instruments like CloudTrail that data admin actions throughout the cloud property. Crucial for incident investigation, compliance, and publicity of dangerous insider actions.
- API/tokens: Code-based cloud entry by way of API and instruments depend on short-lived generated tokens. Provides protections in comparison with simply user-based interactive logins.
Strong IAM is vital to cloud system safety as a result of it dictates who can penetrate cloud environments no matter infrastructure safety defenses. Get IAM improper and all of your safety measures might grow to be susceptible. However should you implement privilege entry, backups, and encryption, the remaining grow to be exponentially simpler since IAM cuts off unauthorized entry on the roots.
9. Require Multi-factor Authentication (MFA)
Increasing additional on entry controls, one extremely helpful mechanism to include is multi-factor authentication (MFA) implementing a number of strategies of verifying identification.
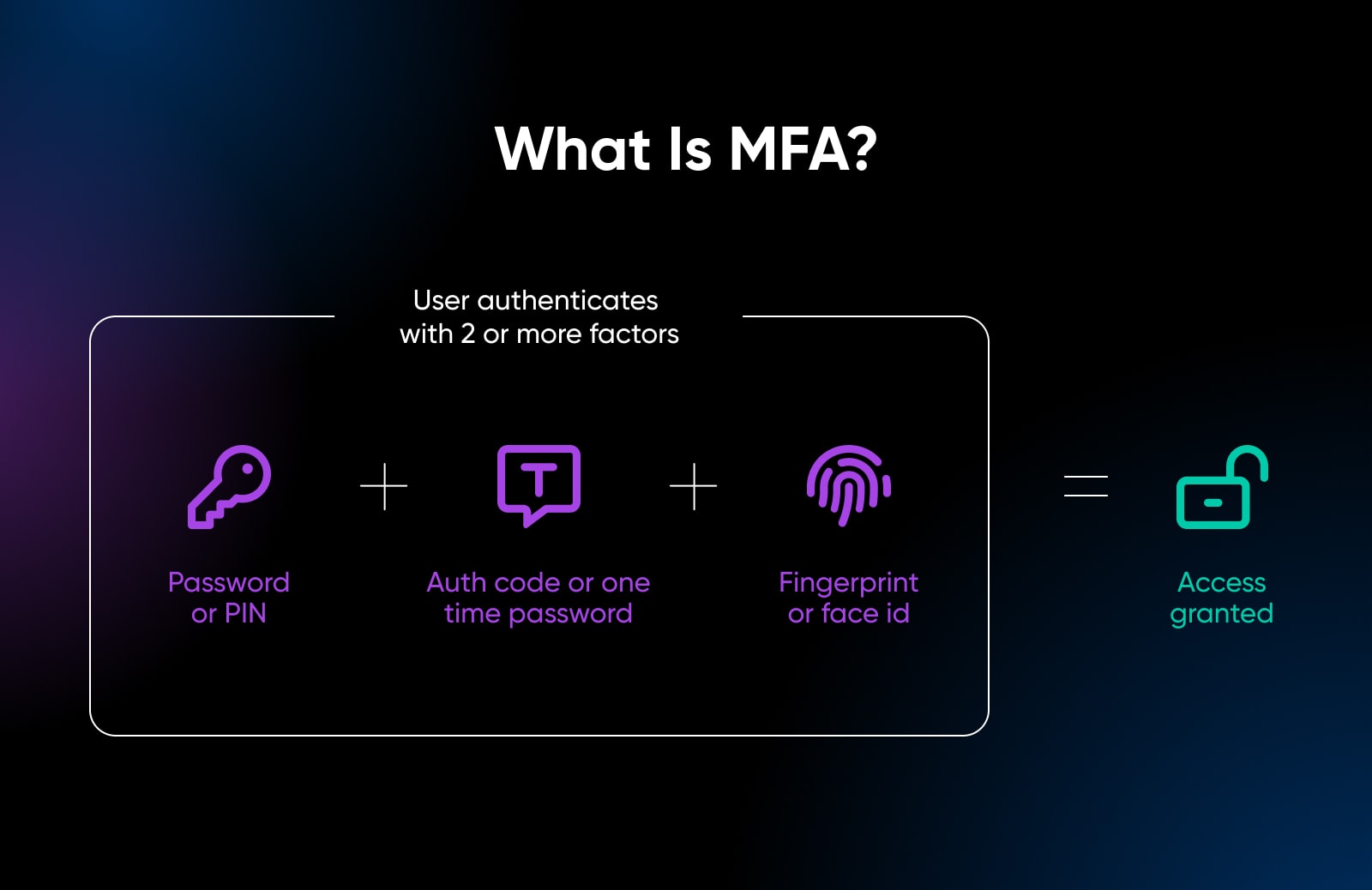
The place single-factor authentication depends on only one credential, like passwords, MFA capitalizes on customers having a number of validation strategies of their possession by requiring any two or extra to completely authenticate classes. This minimizes impersonation dangers considerably, even when one issue is compromised.
Widespread examples embrace:
- Requiring a one-time verification code despatched by way of SMS/e mail together with username/password entry.
- Utilizing a {hardware} token or authenticator app to generate rotating codes.
- Leveraging biometrics like fingerprint scans or facial recognition on cell.
- Answering safety questions preset by the person.
So even when a cloud console password is guessed accurately by way of brute pressure, with out intercepting the person’s cellphone for SMS tokens, the session can not progress. That is why DreamHost accounts may be secured with MFA— This added barrier can deter automated assaults, leaving them on the lookout for a better goal.
10. Safe Endpoints That Entry The Cloud
To this point our information safety strategies have centered on securing the cloud infrastructure itself in addition to entry channels into it. Nevertheless, we have to think about threats that originate from compromised endpoints, which then hook up with cloud environments.
If laptops and workstations lack anti-virus protections for instance, malware may pivot from them into in any other case well-hardened cloud servers. That’s the reason endpoint safety safeguards combine tightly with cloud entry insurance policies as one other vital layer of defense-in-depth.
Widespread endpoint hardening strategies contain:
- Putting in respected anti-virus/anti-malware instruments.
- Deploying endpoint detection & response (EDR) for added monitoring.
- Enabling host-based firewalls and intrusion detection methods.
- Sustaining patching and safety updates promptly.
- Monitoring asset inventories with agent software program.
- Prohibiting admin privileges on finish person units.
- Imposing drive encryption by way of Bitlocker.
- Blocking unauthorized peripheral units like USB storage.
- Securely configured net proxies and DNS filtering.
11. Prioritize Safety Consciousness And Coaching
After discussing the varied technical and procedural safeguards to safe cloud information, we now contact upon what is commonly the most important vulnerability: the human component.
As a lot as we architect layered defenses like firewalls, IAM, encryption, and hardening to guard cloud infrastructure, none of these matter if customers themselves have interaction in dangerous practices whether or not deliberately or unintentionally.

Some frequent examples embrace:
- Reusing passwords throughout private and work accounts.
- Opening phishing emails and malicious attachments.
- Not vetting hyperlinks earlier than clicking them.
- Storing passwords in insecure recordsdata or notes.
- Discussing confidential information over insecure channels.
- Failing to logout of cloud service accounts after utilization.
- Saving recordsdata containing delicate information in public cloud storage buckets.
The listing goes on. No technical controls can totally compensate for lack of safety consciousness amongst groups working cloud platforms day-to-day. That makes ongoing schooling the strongest defend by cultivating a self-reinforcing tradition of safety.
Implement formal safety consciousness coaching packages ought to deal with:
- Simulated phishing: Trains employees to establish and keep away from actual world phishing lures focusing on cloud credentials and information. Improves menace literacy.
- Safe practices: Gives steerage on password hygiene, social engineering pink flags, dealing with delicate information, correct cloud utilization and extra. Units utilization Expectations.
- Cloud dangers: Highlights frequent cloud-specific vulnerabilities like misconfigurations, entry creep and information leaks so employees higher comprehend implications of their obligations.
- Compliance necessities: Outlines insurance policies for entry administration, third events dealing with information and utilization laws. Maintains compliance.
- Incident reporting: Encourages confidential reporting of suspected violations or breaches noticed. Enhances visibility.
“No password, passkey, password supervisor, or two-factor authentication *alone* can defend you from social engineering. Social engineers goal us as people first and the know-how we use second. We should perceive that technical options alone are usually not going to offer good safety.”
— Dr. Martin Kraemer, Safety Consciousness Advocate, KnowBe4
Annual or bi-annual refresher coaching mixed with steady teaching nurtures a security-focused organizational tradition the place cloud customers higher admire protected information dealing with.
12. Monitor Service Supplier Safety Posture
Final however actually not least, a dimension of cloud safety that always will get ignored is administration of safety offered by the cloud service supplier itself.
“Monitoring is necessary as instruments don’t work 100% by itself. Have a third-party or a staff to investigate alerts and reply to incidents. That is the most effective [way] to enhance your safety and safeguard your data property.”
— Felipe Mafra, CISO North America at Thales GTS
Whereas discussions round encryption, entry administration and the like deal with controls instantly managed by us, the cloud supplier additionally implements foundational protections for the information facilities, networks and {hardware} infrastructure underpinning our laptop environments.
Examples of safety measures applied by suppliers embrace:
- Bodily information middle protections like fences, video surveillance and guards.
- Biometric authentication for information middle entry.
- Redundant energy and backups to safe infrastructure.
- Hardened hypervisors separating buyer cases.
- DDoS mitigation for networks.
- Common third celebration audits.
So whereas we govern safety of the cloud workloads deployed, we should additionally periodically overview safety posture maintained by the service supplier notably referring to any shared accountability areas.
You can begin by:
- Reviewing supplier audit certifications.
- Monitoring advisory notices for rising threats impacting companies.
- Analyzing supplier worker screening and information dealing with insurance policies.
Transfer To The Cloud Fearlessly, With DreamHost
Your information is your small business. It’s the work that you simply’ve spent years constructing. That’s why it’s so necessary to maintain your information safe, particularly when it’s saved within the cloud. The concepts we coated on this article are a superb start line on your cloud-based information safety.
However right here’s the factor: protecting your information safe isn’t nearly following an inventory of guidelines. It’s about being vigilant, about being conscious of the dangers, and about taking steps to guard your self.
The reality is that information is as beneficial as oil, and hackers wish to steal as a lot as they’ll. They usually’re solely getting higher at what they do. That’s why you additionally want a service supplier that helps implement safety finest practices when you do what you do finest — develop your small business.
DreamHost focuses on safety and backups, so you’ll be able to relaxation assured that your beneficial work isn’t in useless if a safety incident does happen. For those who’re contemplating a cloud service supplier on your challenge, strive DreamHost at this time.
DreamObjects is an affordable object storage service nice for internet hosting recordsdata, storing backups, and net app growth.

[ad_2]